Securing Your ArcGIS Maps: A Government IT Director's Guide to Preventing Accidental Data Exposure
Government GIS infrastructure contains sensitive data including facility locations, utility networks, and emergency routes. Here's how to prevent accidental data exposure.

Government GIS infrastructure contains sensitive data including facility locations, utility networks, and emergency routes — targets for adversaries. An October 2025 breach saw Chinese state-sponsored hackers maintain ArcGIS server access for over a year through weak administrator credentials.
The Stakes: Why GIS Security Matters for Government
Government mapping systems contain critical infrastructure coordinates, emergency response data and evacuation routes, facility information and security details, utility network topology, and sensitive planning data. CISA has warned of increasing nation-state targeting of GIS systems.
Case Study: Flax Typhoon ArcGIS Compromise
A sophisticated attack succeeded through weak passwords on a portal administrator account. The connection between public portal and internal servers created lateral access, and attackers weaponized Java Server Object Extensions to function as web shells, disguising malicious traffic as routine operations. The attack went undetected for over 12 months, and malware embedded in backups complicated recovery.
Common ArcGIS Misconfigurations
Overly Permissive Sharing Settings — Users can inadvertently expose sensitive feature layers by sharing with “Everyone.” Esri’s Public Data Collection setting provides safeguards but remains underutilized.
Weak Authentication Practices — Weak passwords, missing multi-factor authentication, shared accounts, exposed API keys in repositories, and long-lived tokens without expiration.
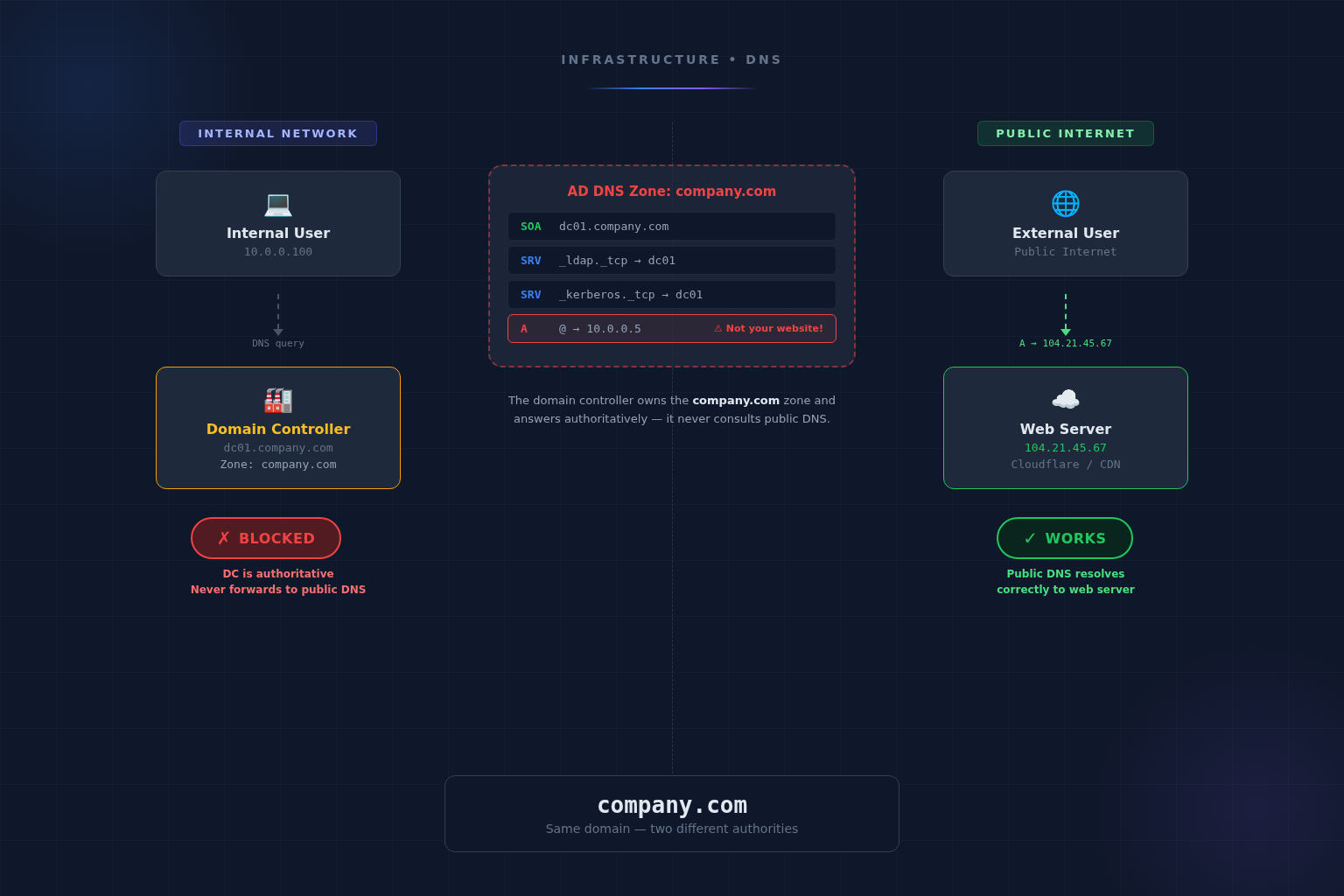
Network Architecture Issues — Many deployments connect public-facing portals directly to internal servers without Web Application Firewall protection or adequate segmentation.
Outdated Software — Esri releases regular security patches addressing reflected XSS, server-side request forgery, directory traversal, and authentication bypass vulnerabilities.
Security Hardening Checklist
Enforce MFA on administrative accounts. Implement strong 16+ character passwords. Apply the principle of least privilege. Audit admin access quarterly. Rotate API keys every 90 days. Run security scanning tools monthly. Audit all publicly shared items. Deploy a Web Application Firewall. Segment public portals from internal servers. Subscribe to Esri security advisories and apply critical patches within 14 days.
Conclusion
GIS security requires continuous practice rather than one-time configuration. Monthly security scanning, quarterly credential rotation and access audits, and annual comprehensive assessments should be standard practice. Nation-state actors view government mapping systems as high-value intelligence targets — security posture should reflect this threat reality.
More from the blog
Want to discuss this topic?
Our team is available to talk about AI strategy, security, and digital transformation.