How Spammers Exploit CloudFlare Zero Trust to Bypass Bot Protection (And How We Stopped Them)
Spam bots were exploiting CloudFlare Zero Trust infrastructure to circumvent bot protection. Here's how we achieved an 85% reduction in spam with a multi-layered defense strategy.

In October 2025, Fruition discovered that spam bots were exploiting CloudFlare Zero Trust infrastructure to circumvent bot protection measures. We received 200-300 spam submissions daily despite having robust CloudFlare security enabled. Through a multi-layered defense strategy, we achieved an 85% reduction in spam without degrading user experience.
The Problem
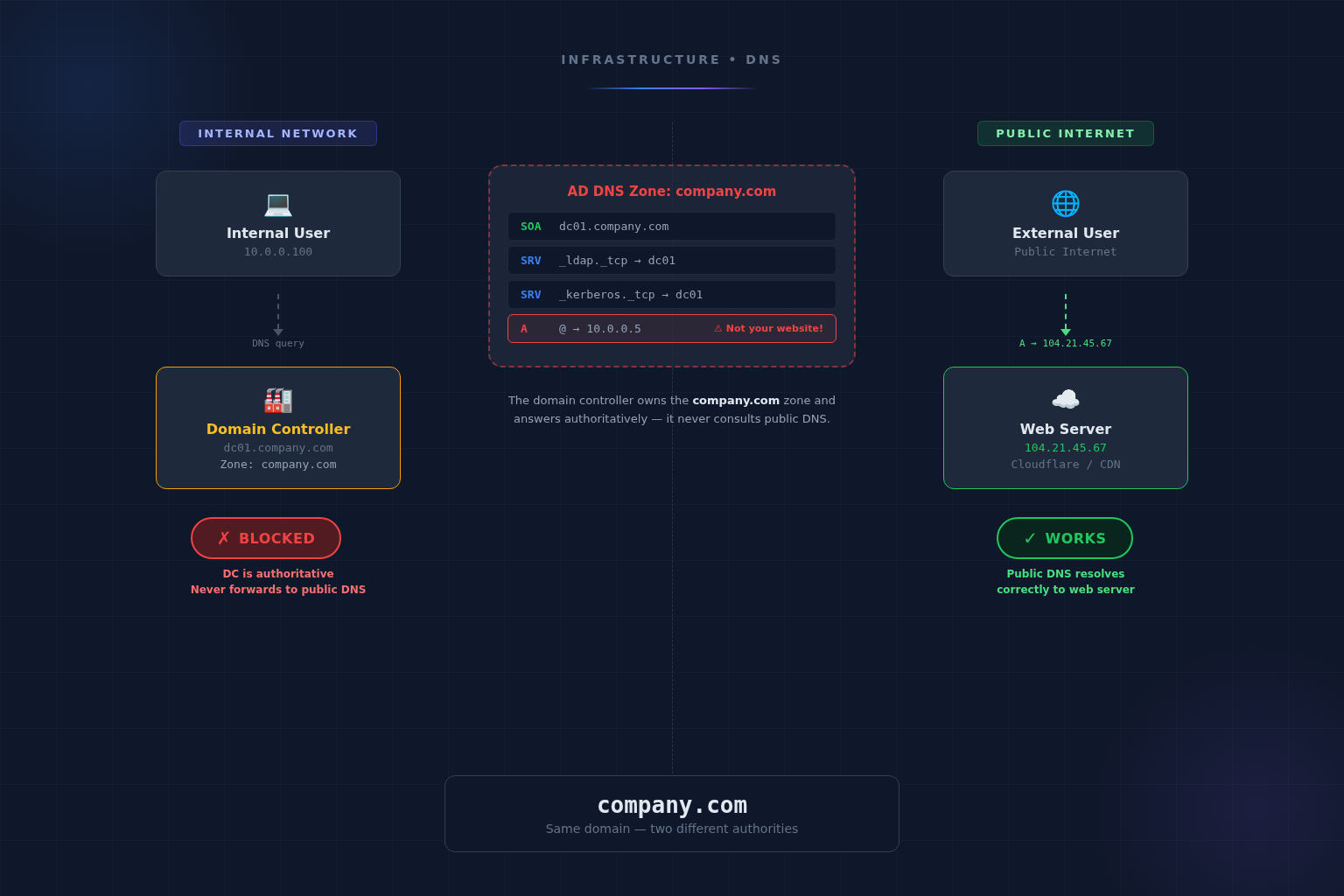
Despite active Bot Fight Mode, high security levels, and basic honeypot fields, spam continued unabated. Investigation revealed that source IPs originated from CloudFlare’s own IP ranges, suggesting attackers were routing traffic through CloudFlare Zero Trust/WARP to appear as trusted internal traffic.
Why Traditional Defenses Failed
IP-based blocking failed because attackers rotate through CloudFlare’s extensive IP pool. User-Agent filtering failed because modern bots employ legitimate browser signatures. Keyword filtering failed because spammers adapt with creative variations. And honeypot fields failed because sophisticated bots detect hidden form elements.
Our Three-Layer Solution
Layer 1: CloudFlare Turnstile — An invisible CAPTCHA alternative that validates browser behavior rather than IP reputation. It detects headless browsers and automation frameworks while remaining undetectable to users.
Layer 2: Time-Based Validation — Forms record load timestamps and reject submissions occurring too quickly (under 3 seconds) or after sessions expire (beyond 30 minutes). This captures the inherent human pattern of reading and completing forms.
Layer 3: Rate Limiting — Restricts submissions to three per email address per hour, preventing bulk campaigns while accommodating legitimate resubmissions.
Results
- Spam submissions: Reduced from 200-300 daily to 20-30 daily
- Legitimate submissions: Remained stable at approximately 10 daily
- Overall spam reduction: 85%
- False positives: Zero reported
- User experience impact: Imperceptible
Key Takeaways
Trust behavior over origin — network source alone cannot guarantee legitimacy. Invisible security minimizes user friction. Defense-in-depth proves more effective than single-layer approaches. And behavioral validation represents the future of security as attackers gain access to VPNs and proxy networks.
More from the blog
Want to discuss this topic?
Our team is available to talk about AI strategy, security, and digital transformation.